DoS (Denial of Service) is a type of cyber attack that aim at disrupting, stopping the services of a server that is connected to the Internet, and it prevents the main users from accessing the network resources. DoS attacks can cause material and moral damage to the institution using the system by preventing the real users such as clients, members and staff from accessing the system. Even though DoS attacks do not usually result in the theft of important information, they can cause great damage since they disrupt operations.
In DoS attacks, a computer tries to slow down the server by either sending information to a server connected to the Internet that will slow down the network, or increasing the traffic in the target server.
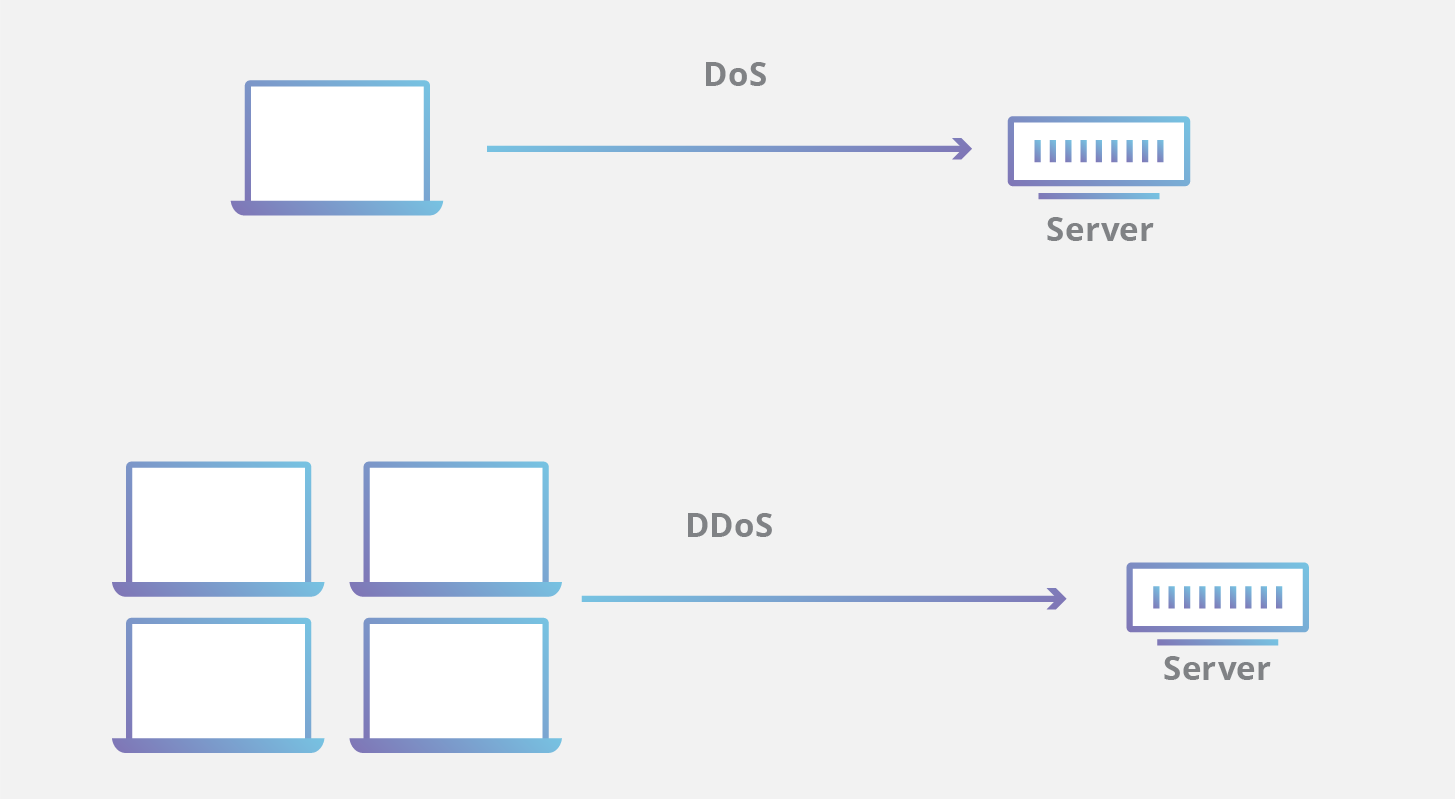
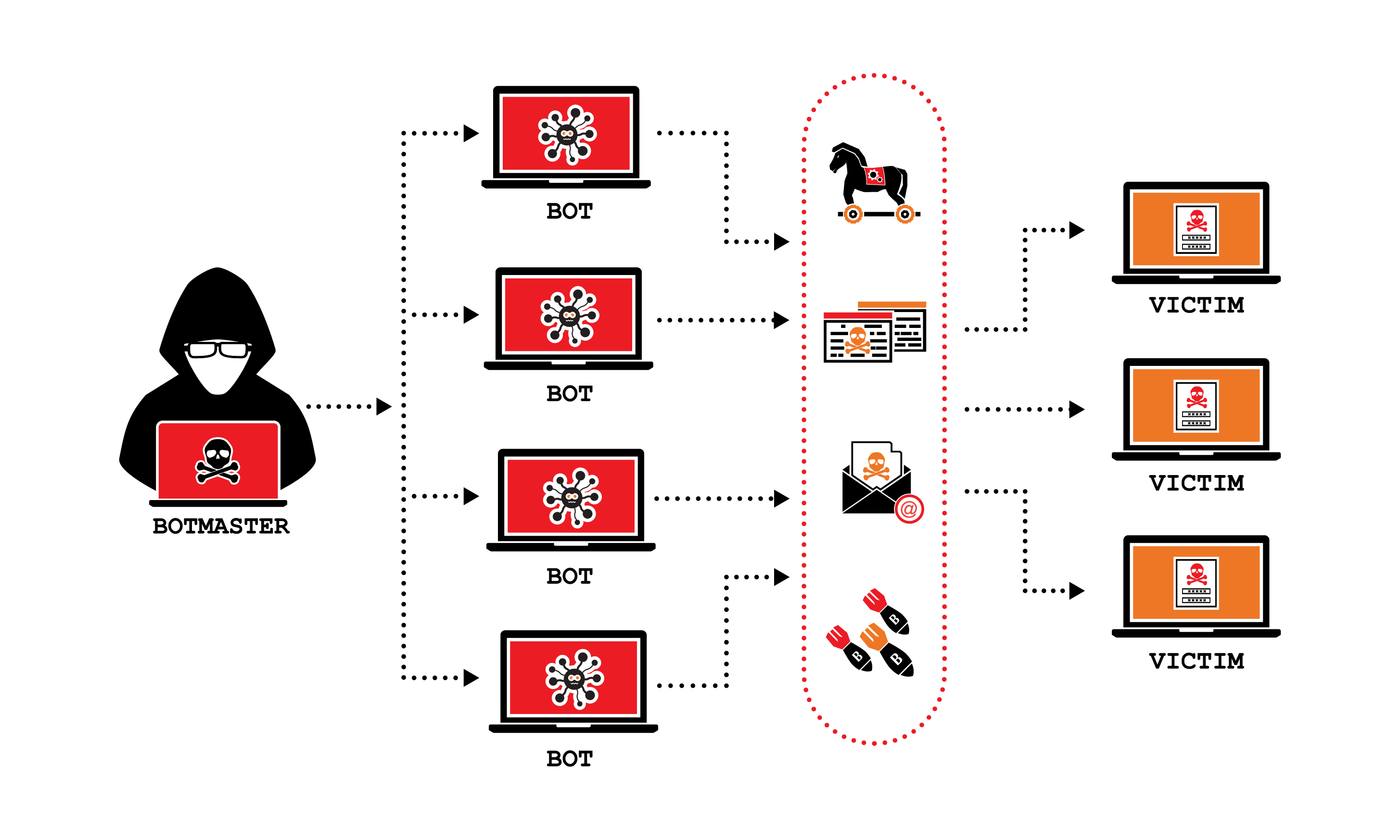
DDoS (Distributed of Denial Attack) attack is a type of cyber attack aimed at slowing down a server by sending simultaneous requests to a server from computers that are located in multiple locations. The most important difference from DoS attack is that multiple computers in different locations are used in the attack.
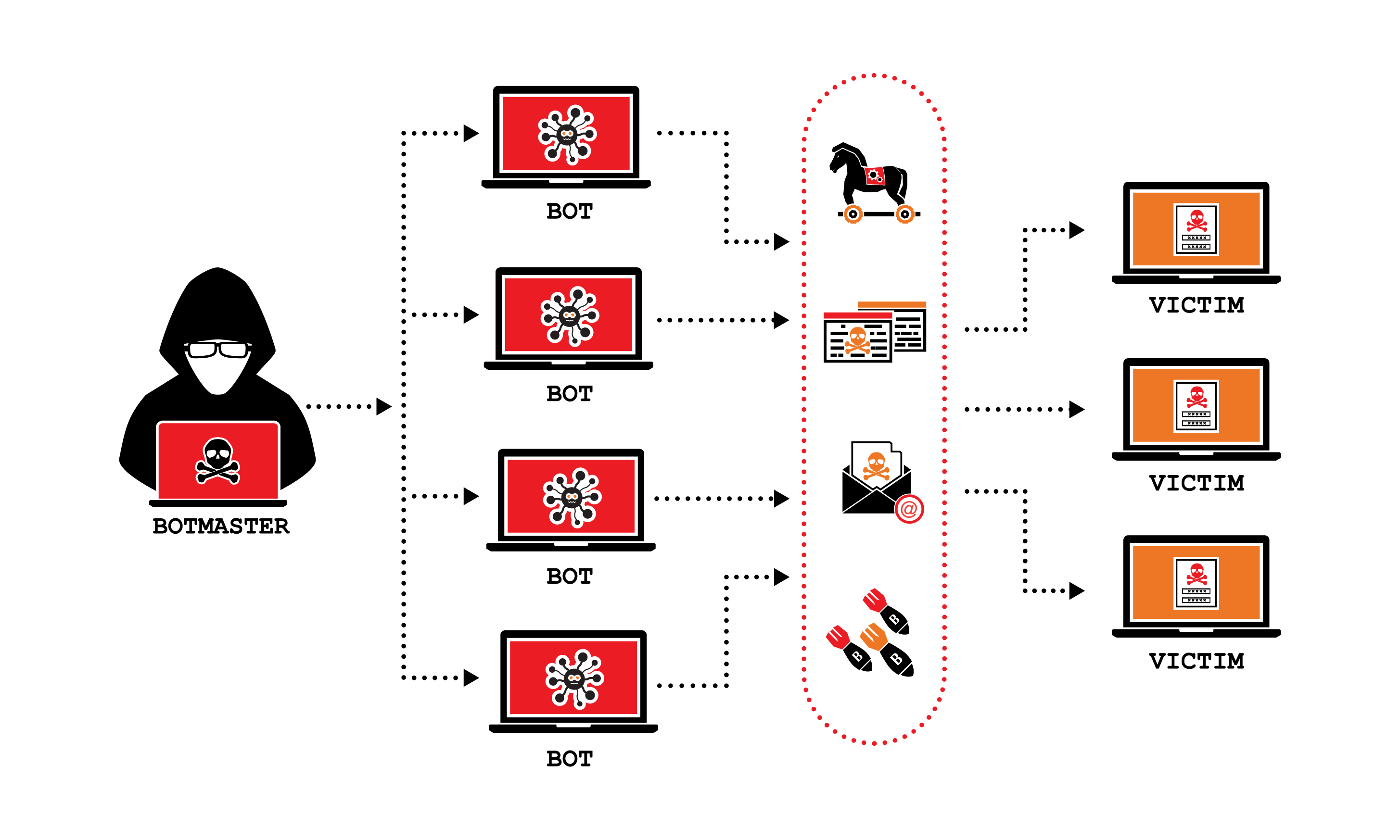
Before the attack, users' computers are secretly hijacked with infected software written by hackers. In this way, zombie computers are prepared for DDoS attacks. A DDoS attack can be even more effective with an increase in the number of computers that virus software enters.
Zombie computers that look real in DDoS attacks try to connect to the server that is connected to the Internet simultaneously. The increase in the number of computers trying to connect will increase the requests sent to the server at the same time, and after a while, the server, which cannot respond to the requests, crashes. In this way, the DDoS attack will achieve its purpose.
DoS and DDoS attack which usually target e-commerce, bank and government systems, cause great damage to their victims. Recently, with the increase in measures taken against these attacks and the effect of deterrent laws, the impact and number of attacks have begun to decrease. Of course, this does not mean that DoS and DDoS attacks will end.
That's all I had to share in the field of cyber security today. Thank you for your time. Take care of yourselves.




Yorumunu Bırak
Comments
0 CommentsHenüz yorum yapılmamış. İlk yorum yapan sen ol.