Now let’s take a closer look at these methods one by one.
Shoulder surfing is obtaining (stealing) information about someone by peeping them. The thing we need to be careful about this is making sure no one is watching us when we are using an online banking application or typing a password at a public place like busses, airports or etc. We can lower the brightness of our screen or cover our screen.

The things that you think are unimportant and threw away may be substantial information for a social engineer. They can get information from the things you throw away like documents with typos, phone numbers, notes. They can collect these and put them together like a jigsaw puzzle and learn information about you.
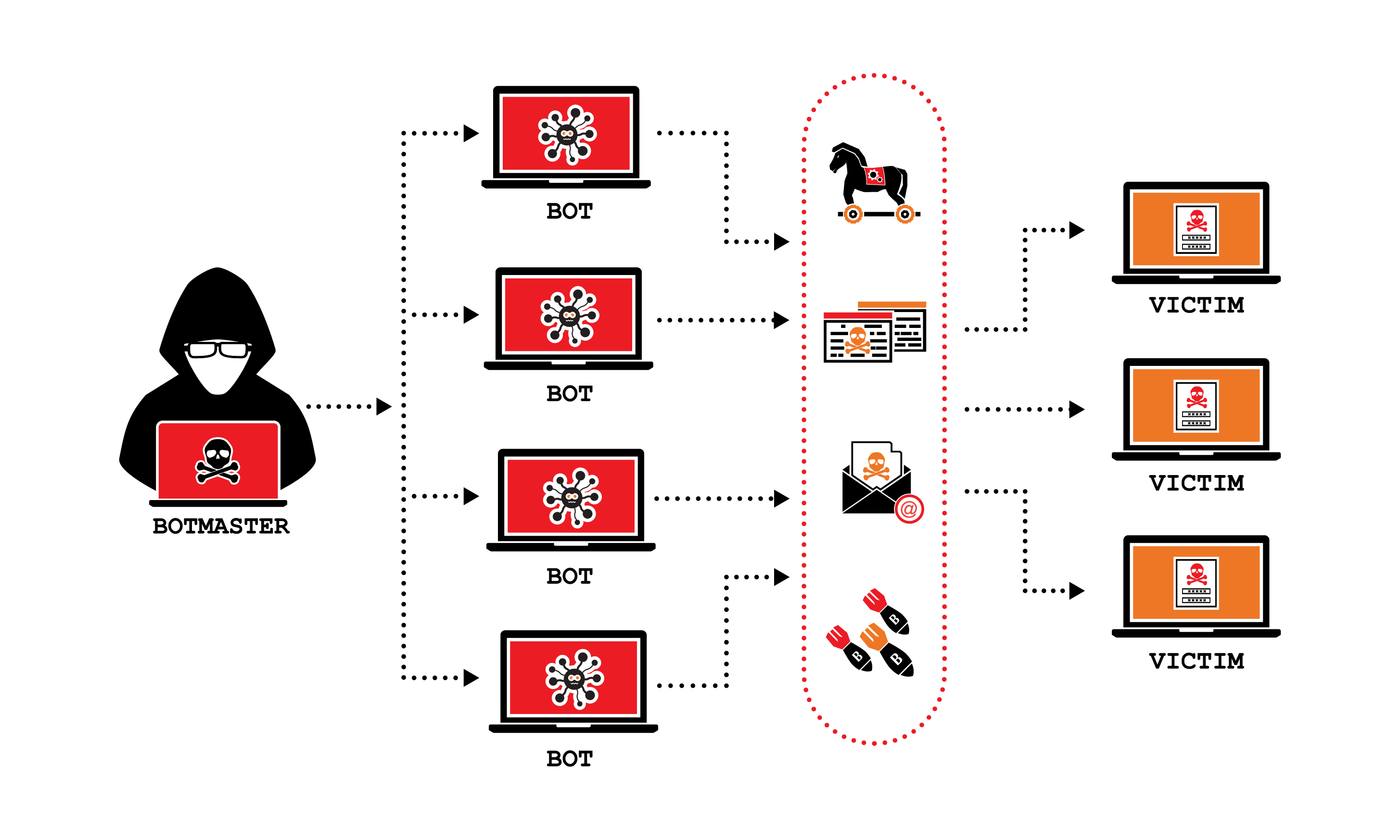
Trojan virus is a malicious code or software that can look legit but can take control of your computer. It is designed to damage, corrupt, steal or harm your data or network. Unlike other viruses it cannot reproduce by infecting other files or computers. Although Trojan can too infect via the things you download like other viruses.

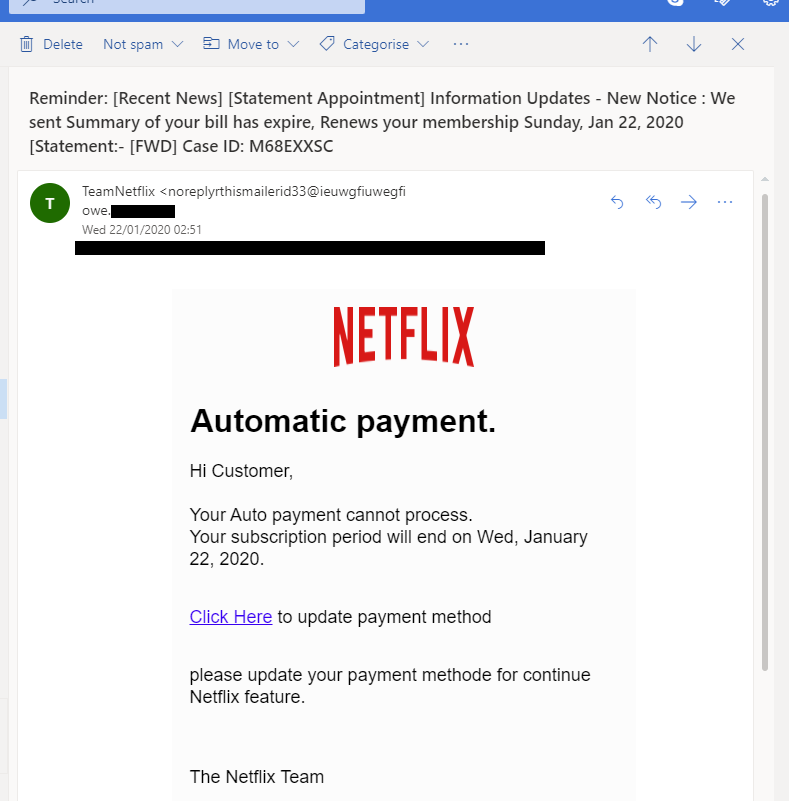
Phishing is a very common method of getting information and it also can run codes on the opposite computer and turn it into a zombie computer.
This is an example of phishing. Here, the predator wants the victim to enable the automatic payment system so that he can get the victim’s credit card information. There are two ways to know that this email is fake. One of them is that the sender of the email is not Netflix’s official email address. And the second way is when you click the link, the URL of the page that opens is different than Netflix’s. It is important to know that it is a phishing situation in the first try, we must be very careful.






Yorumunu Bırak
Comments
0 CommentsHenüz yorum yapılmamış. İlk yorum yapan sen ol.